IoT has quickly moved from a niche concept to a significant part of modern technollogy and system design. Today, we’re dealing with networks of interconnected devices that span everything from edge hardware to cloud platforms, all working together in real time.
As these systems grow, so does the need to design them thoughtfully. To have them go beyond functionality… for long-term reliability and durability. It’s no longer enough to simply connect devices; the focus has shifted toward building systems that can handle complexity in a structured way.
In this blog, we take a look at IoT security closely, breaking down the key challenges and solution approaches from a technical perspective.
What exactly are IoT Security Issues?
IoT security issues refer to the vulnerabilities and risks that arise in connected device ecosystems. In this space, there are several elements that continuously exchange data, such as:
- Sensors,
- Embedded systems,
- Gateways,
- Cloud services
IoT environments are highly distributed and often operate with limited computing resources, which makes it harder to enforce consistent security controls across all layers. These issues can affect the integrity and availability of both device-level operations and the larger network they are a part of.
What causes Security Issues in IoT Devices?
Several technical factors are responsible for rising security vulnerabilities in IoT devices, and most of them originate from design trade-offs made for cost and performance.
A major cause is the use of resource-constrained hardware, which limits the ability to implement strong encryption or continuous monitoring mechanisms. This often leads to simplified or weakened security implementations. Just like this, we have many other factors that result in weaker security because often businesses are just rushing to launch products. They forget to pay attention to security issues that may arise later.
This is the biggest reason why many businesses find that their IoT devices aren’t doing as well as they thought.
What are the Risks and Challenges in IoT Security Issues?
Technology is a miscellaneous yet predictable sector. If you look at the industry in a strategic way, you’ll learn that most risks and challenges related to security, even in IoT, can be avoided in the beginning. All you need is to be more aware of the challenges and risks involved in IoT security issues. This is how you’ll be able to prevent them later. Let’s take a look at some of the prominent security issues in IoT:
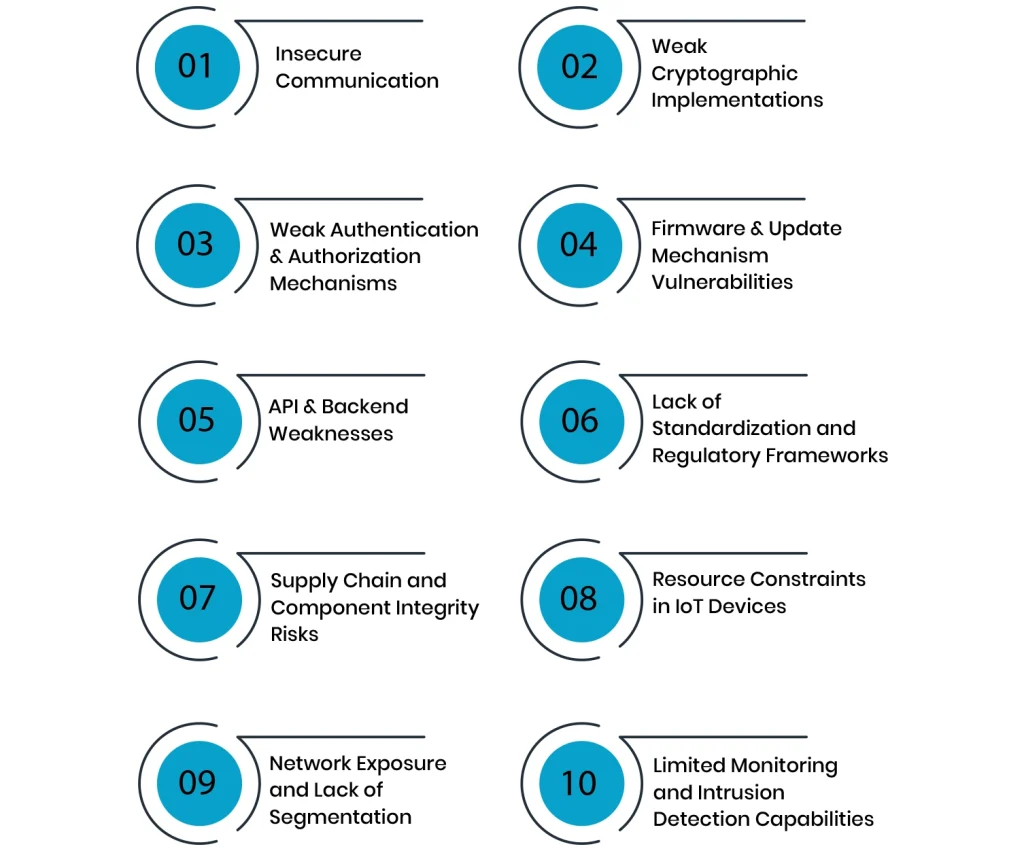
Insecure Communication
Insecure communication in IoT systems arises when data is transmitted between devices and cloud services without proper protection mechanisms. This could include encryption problems or even tighter security. Many IoT deployments rely on lightweight communication protocols that prioritize speed and low power consumption over security.
This becomes a major challenge because attackers can intercept or replay data during transmission. This can lead to man-in-the-middle attacks or leakage of sensitive operational data.
Weak Cryptographic Implementations
Weak cryptographic implementations occur when IoT devices use outdated algorithms or implement encryption libraries incorrectly. In some cases, devices rely on hardcoded cryptographic keys or insufficient entropy sources. This basically makes encryption predictable or easy to break.
The challenge here is the misuse of encryption. Even when encryption is present, improper implementation can give a false sense of security while letting attackers to decrypt or manipulate data.
Weak Authentication & Authorization Mechanisms
Weak authentication and authorization typically result from the use of default credentials. Moreover, the lack of multi-factor authentication or poorly designed access control models further worsens this. Many IoT devices are deployed with factory-set usernames and passwords that are never changed.
This becomes a critical issue because compromised credentials can allow attackers to take full control of devices or move laterally within a network.
Firmware & Update Mechanism Vulnerabilities
Firmware and update vulnerabilities occur when devices lack authenticated update processes or fail to validate firmware integrity before they’re installed. In some cases, updates are transmitted without encryption or signature verification, allowing malicious firmware to be injected.
This is a serious challenge because IoT devices often operate for long periods without manual intervention.
API & Backend Weaknesses
API and backend weaknesses arise when cloud services and APIs supporting IoT devices are not properly secured. In this case, broken authentication and poor input validation are very common issues. These weaknesses are dangerous because IoT devices depend heavily on backend infrastructure.
If an attacker compromises an API, they can potentially access large volumes of device data or issue unauthorized commands.
Lack of Standardization and Regulatory Frameworks
The IoT ecosystem lacks universally enforced security standards. This naturally leads to inconsistent implementation practices across manufacturers and platforms. Each vendor may follow different security models. This lack of standardization creates challenges with integration and security gaps.
Without a unified regulatory framework, enforcing security requirements becomes difficult, resulting in uneven protection levels across IoT deployments.
Supply Chain and Component Integrity Risks
Supply chain risks arise when hardware or software components are compromised before the launch takes place. This can include malicious firmware injection or vulnerabilities introduced through third-party libraries.
These risks are difficult to detect during the launching phase because they originate before the device even reaches production environments.
Resource Constraints in IoT Devices
IoT devices often operate with limited CPU and power resources, which restricts their ability to run complex security mechanisms. As a result, lightweight or simplified security implementations are commonly used.
This becomes a challenge because strong cryptographic algorithms and advanced intrusion detection systems may be too resource-intensive.
Network Exposure and Lack of Segmentation
Many IoT devices are deployed on flat networks without proper segmentation or isolation from critical systems. This means that once a device is compromised, attackers can potentially move laterally across the network.
The challenge is amplified in environments where IoT devices are deployed at scale, such as smart homes or industrial systems.
Limited Monitoring and Intrusion Detection Capabilities
IoT environments often lack powerful monitoring and intrusion detection systems due to device limitations or deployment complexity. Many devices generate minimal logs or lack visibility into runtime behavior.
This creates a risk because problems arise in detecting and responding to attacks in real time. Without proper monitoring, malicious activity can go unnoticed for extended periods.
How Can You Prevent Or Solve These IoT Security Issues?
The challenges can be prevented and even solved if you discover how easy it is to get rid of them. The key is simple: always follow the phrase, “prevention is better than cure”. So, let’s take a look at these solutions in detail:
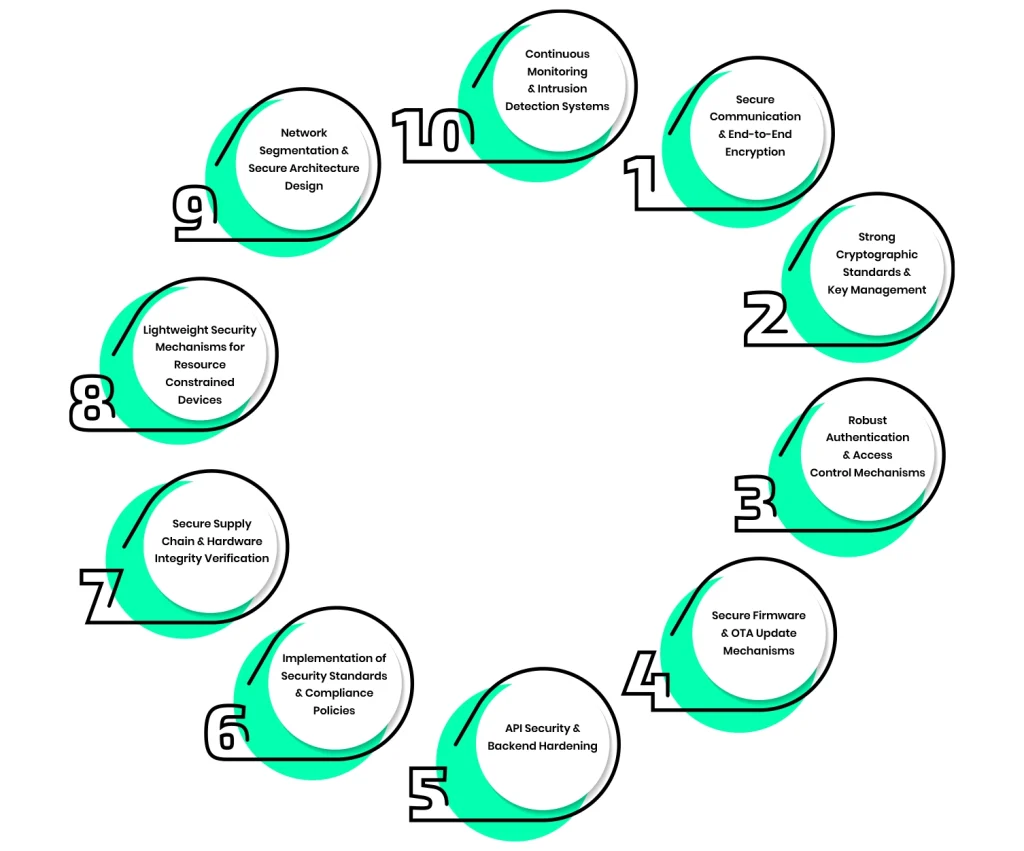
Secure Communication & End-to-End Encryption
Securing communication in IoT systems starts with ensuring that all data in transit is protected using strong encryption protocols such as TLS. This prevents attackers from intercepting or altering sensitive information. End-to-end encryption is further strengthened. How? Well, it does so by ensuring that data remains encrypted throughout its entire journey, not just during transmission.
Strong Cryptographic Standards & Key Management
Strong cryptographic standards ensure that IoT systems rely on modern and well-tested algorithms. To further make this stronger, you can take a few steps like using secure hashing functions and properly generated cryptographic keys. Effective key management is equally important because, without it, even strong encryption can be useless if keys are exposed or reused across multiple devices.
Robust Authentication & Access Control Mechanisms
Powerful authentication ensures that only verified users and devices can access IoT systems, while access control determines what actions each entity is allowed to perform. This typically involves eliminating default credentials and implementing multi-factor authentication where possible.
Secure Firmware & OTA Update Mechanisms
Secure firmware and OTA (Over-the-Air) update mechanisms ensure that devices can safely receive patches and improvements throughout their lifecycle. This requires digitally signing firmware updates and verifying their integrity before installation. This approach prevents attackers from injecting malicious firmware or downgrading devices to vulnerable versions.
API Security & Backend Hardening
API security and backend hardening are important here. They focus on protecting the cloud infrastructure and service endpoints that IoT devices depend on. This includes implementing proper authentication and secure API gateways, while taking any other steps required to make them stronger. Backend hardening ensures that even if attackers target cloud services directly, they cannot exploit weak endpoints or gain unauthorized access.
Implementation of Security Standards & Compliance Policies
Following established security standards and compliance frameworks helps ensure consistent security practices across IoT deployments. Standards such as ISO/IEC guidelines or industry-related frameworks set out basic requirements for secure development and deployment. This reduces inconsistencies between vendors and ensures that systems meet minimum security expectations.
Secure Supply Chain & Hardware Integrity Verification
Securing the supply chain involves ensuring that both hardware and software components are free from tampering before the launch comes across. This includes verifying firmware authenticity and validating hardware integrity during manufacturing and installation.
Lightweight Security Mechanisms for Resource-Constrained Devices
Since IoT devices often have quite limited processing power and memory, security solutions must be optimized. Lightweight cryptographic algorithms and optimized security protocols are designed to provide protection without overwhelming device resources.
Network Segmentation & Secure Architecture Design
Network segmentation involves dividing IoT systems into isolated zones to prevent unrestricted communication between devices and critical infrastructure. This limits the spread of attacks if one device is compromised. Secure architecture design further strengthens this by implementing layered defenses and isolation of sensitive systems.
Continuous Monitoring & Intrusion Detection Systems
Continuous monitoring ensures that IoT environments are constantly observed for unusual behavior or unauthorized access attempts. Intrusion detection systems (IDS) play a key role in identifying potential threats in real time. This allows organizations to respond quickly to security incidents before they escalate.
Conclusion
In the upcoming era, IoT will continue to get more popular. So, it is necessary that we stay focused on reducing and preventing these challenges from growing even further. The real challenge lies in maintaining consistent protection across highly distributed devices and communication pathways while still working within practical constraints.
A well-secured IoT ecosystem depends on applying the right controls at the right layers. When these elements are aligned, IoT deployments become far more resilient to evolving threats without compromising functionality or scale.